TheDocumentation Index
Fetch the complete documentation index at: https://cal.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
OnboardingEmbed atom lets you embed the full Cal.com signup, onboarding, and OAuth authorization flow directly inside your application. Users create a Cal.com account, complete onboarding, and grant your app OAuth access — all without leaving your site.
For a demonstration of the onboarding embed flow, please refer to the video below.
When to use this
Use the Onboarding Embed when you want new users to connect their Cal.com account during your app’s own signup or setup flow. Instead of redirecting users to Cal.com and back, the entire process happens in an embedded dialog.Prerequisites
- An OAuth client created via OAuth setup
- The
@calcom/atomspackage installed in your project
Modes
The component supports two modes for receiving the authorization code:- Callback mode — provide
onAuthorizationAllowedto receive the authorization code via a callback. No page navigation occurs. - Redirect mode — omit
onAuthorizationAllowedand the browser navigates to yourredirectUriwith the code as a query parameter.
After a new user signs up through the embed, Cal.com sends them a verification email to confirm their email address.
Callback mode
ProvideonAuthorizationAllowed to receive the authorization code directly. The dialog closes and your callback fires after the user authorizes your OAuth client — no page reload.
Redirect mode
OmitonAuthorizationAllowed and the browser navigates to your redirectUri after the user completes onboarding and grants access:
Props
| Prop | Type | Required | Description |
|---|---|---|---|
oAuthClientId | string | Yes | Your OAuth client ID. |
host | string | No | Cal.com host URL. Defaults to https://app.cal.com. Used for local development to point to the Cal web app. |
theme | "light" | "dark" | No | Theme for the embedded onboarding UI. Defaults to "light". |
user | { email?: string, name?: string, username?: string } | No | Prefill user details in signup and profile steps. |
authorization | AuthorizationProps | Yes | OAuth authorization parameters (see below). |
onAuthorizationAllowed | (result: { code: string }) => void | No | Called with the authorization code on completion. If provided, enables callback mode. If omitted, enables redirect mode. |
onError | (error: OnboardingError) => void | No | Called on unrecoverable error. |
onAuthorizationDenied | () => void | No | Called when the user declines OAuth authorization. If omitted, the browser navigates to redirectUri?error=access_denied&state=YOUR_STATE. |
onClose | () => void | No | Called when the user dismisses the dialog before completing. |
trigger | ReactNode | No | Custom trigger element. Defaults to a “Continue with Cal.com” button. |
Authorization props
| Prop | Type | Required | Description |
|---|---|---|---|
redirectUri | string | Yes | One of the redirect URIs registered on your OAuth client. Must share the same origin as the page hosting <OnboardingEmbed />, because the iframe uses postMessage for secure communication. |
scope | string[] | Yes | OAuth scopes to request. Must be a subset of scopes registered on the OAuth client. See the OAuth scopes documentation. |
state | string | Yes | CSRF token. Generate a unique value per session and verify it when you receive the authorization code. |
codeChallenge | string | For public clients | PKCE code challenge (S256 method). Required for public OAuth clients. |
If the user signs up via Google, the
user prop values are ignored — name, email, and username are inferred from the Google account instead.Trigger and theme
Thetheme prop controls the appearance of the trigger button, the onboarding steps, and the authorization page. The default trigger renders a “Continue with Cal.com” button:
| Light theme (default) | Dark theme |
|---|---|
 |  |
trigger prop:
User flow walkthrough
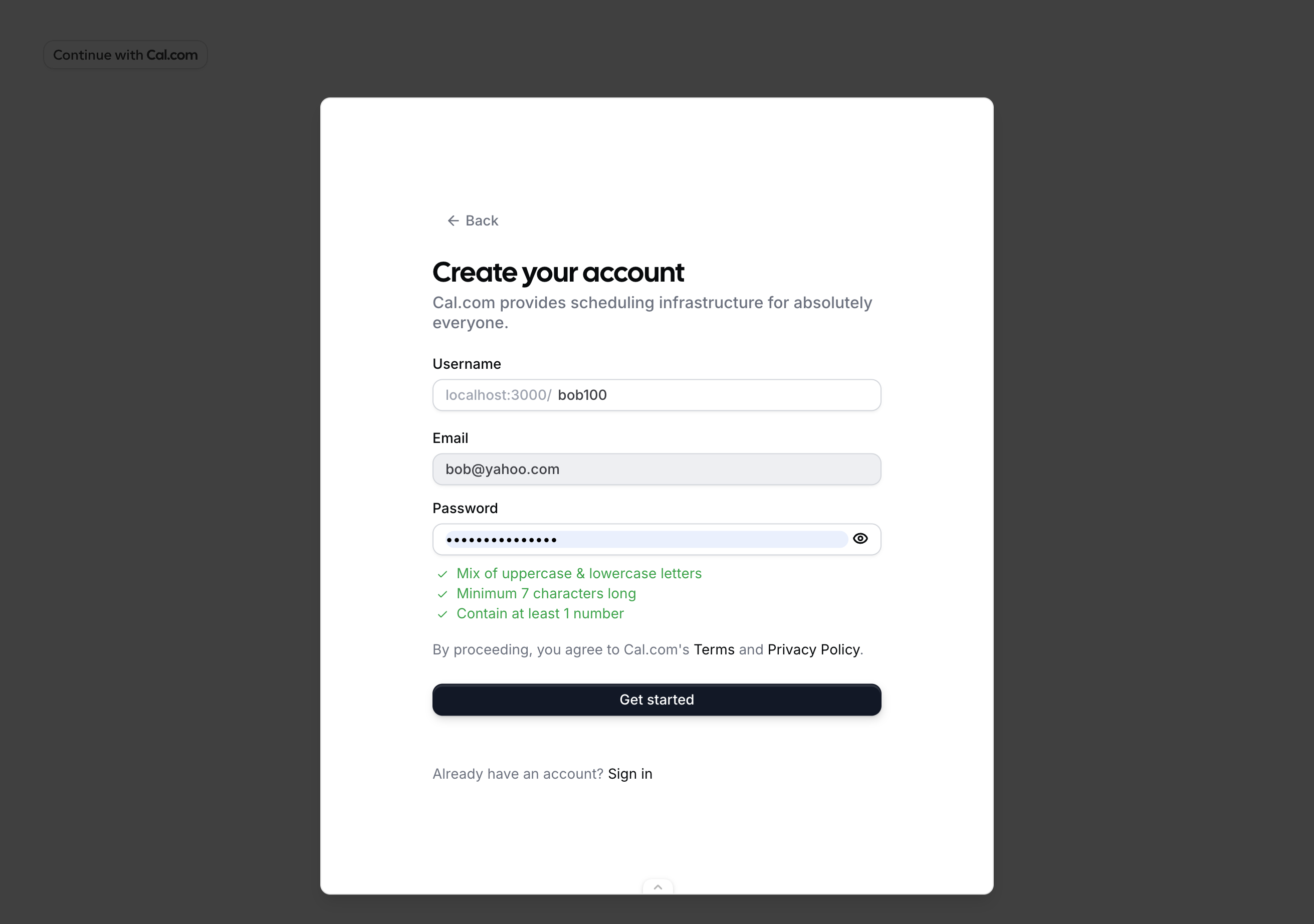
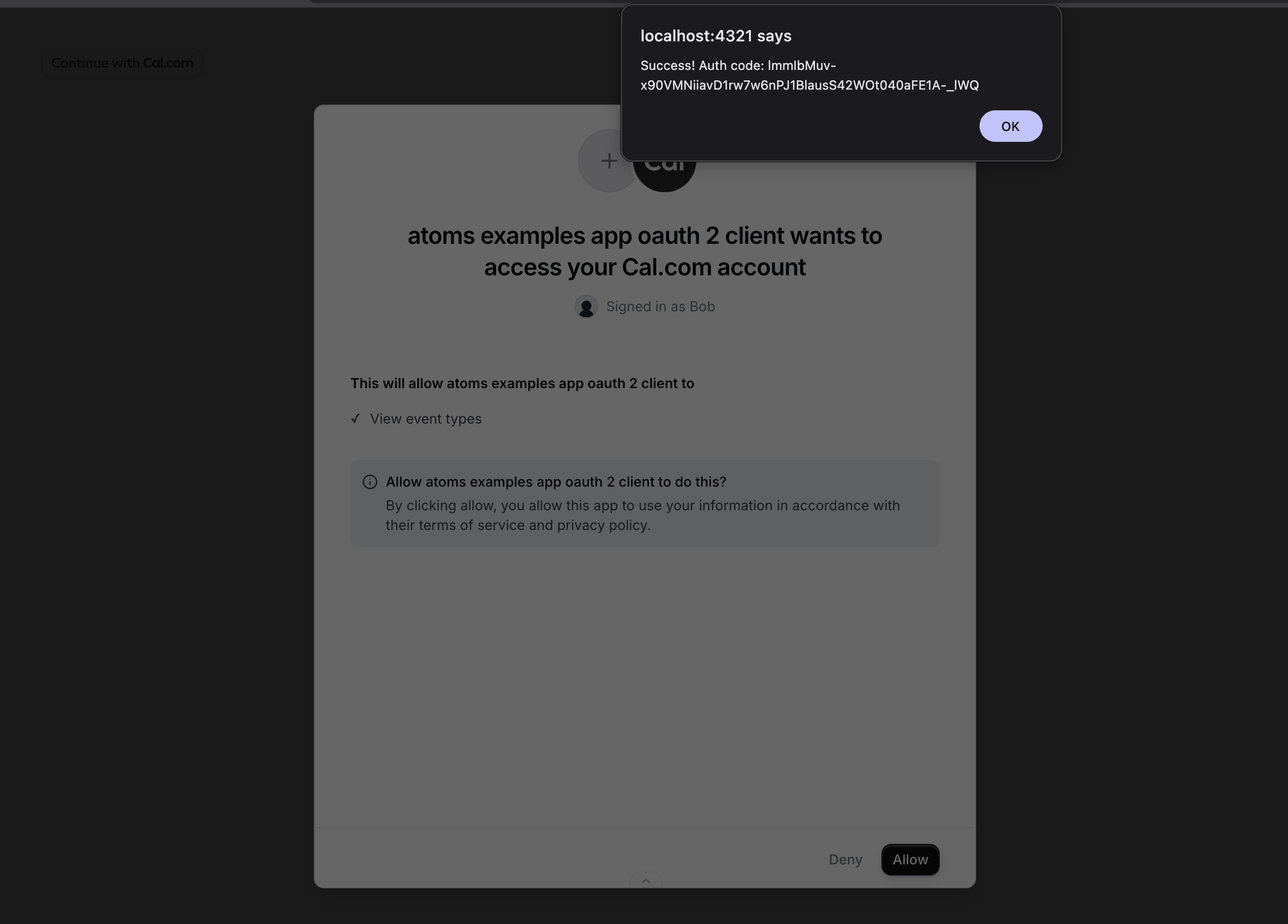
Here’s what happens when a user clicks the trigger withonAuthorizationAllowed provided and the user prop set:
user.email prop prefills the email field.
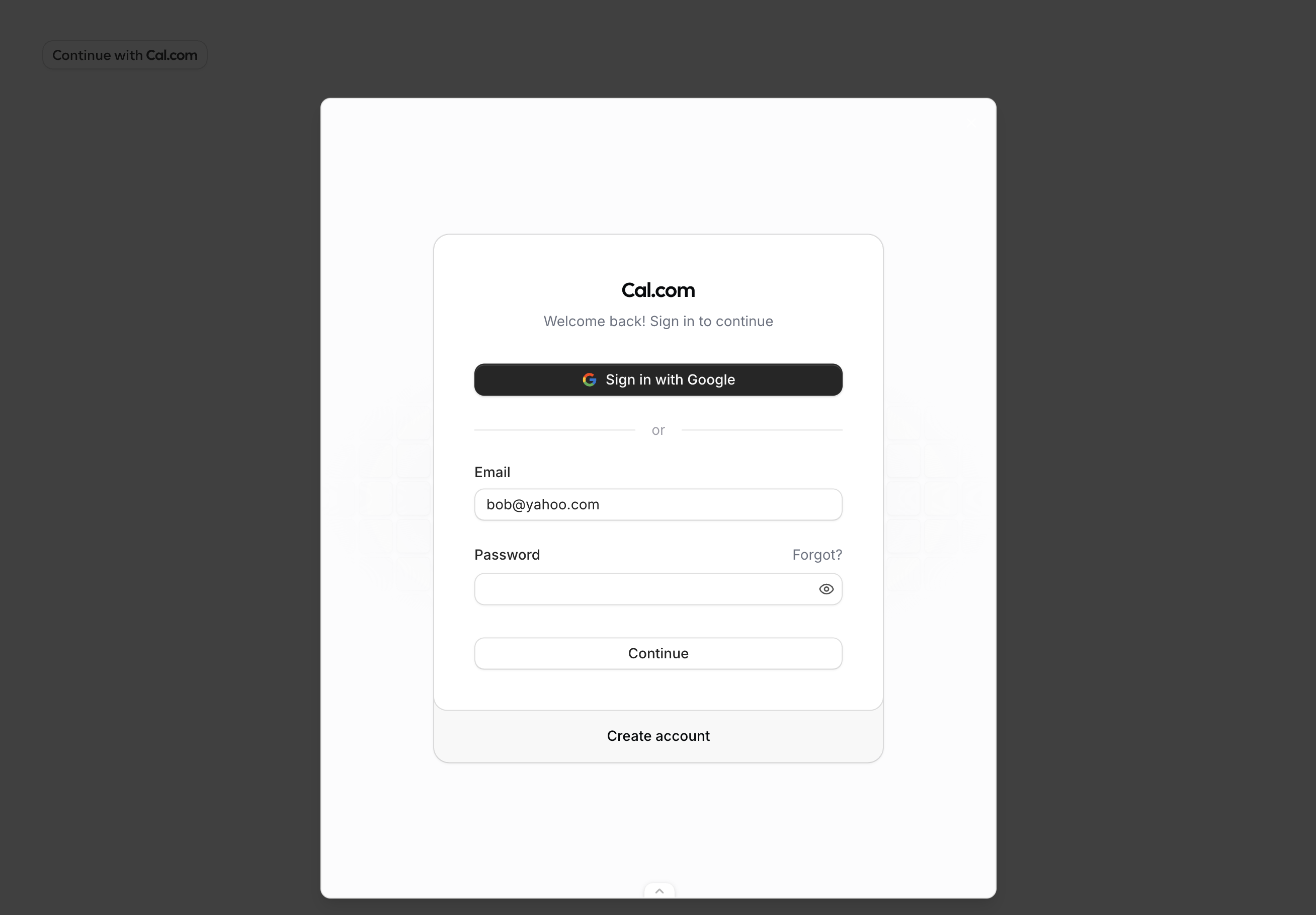
user.email and user.username props are prefilled.
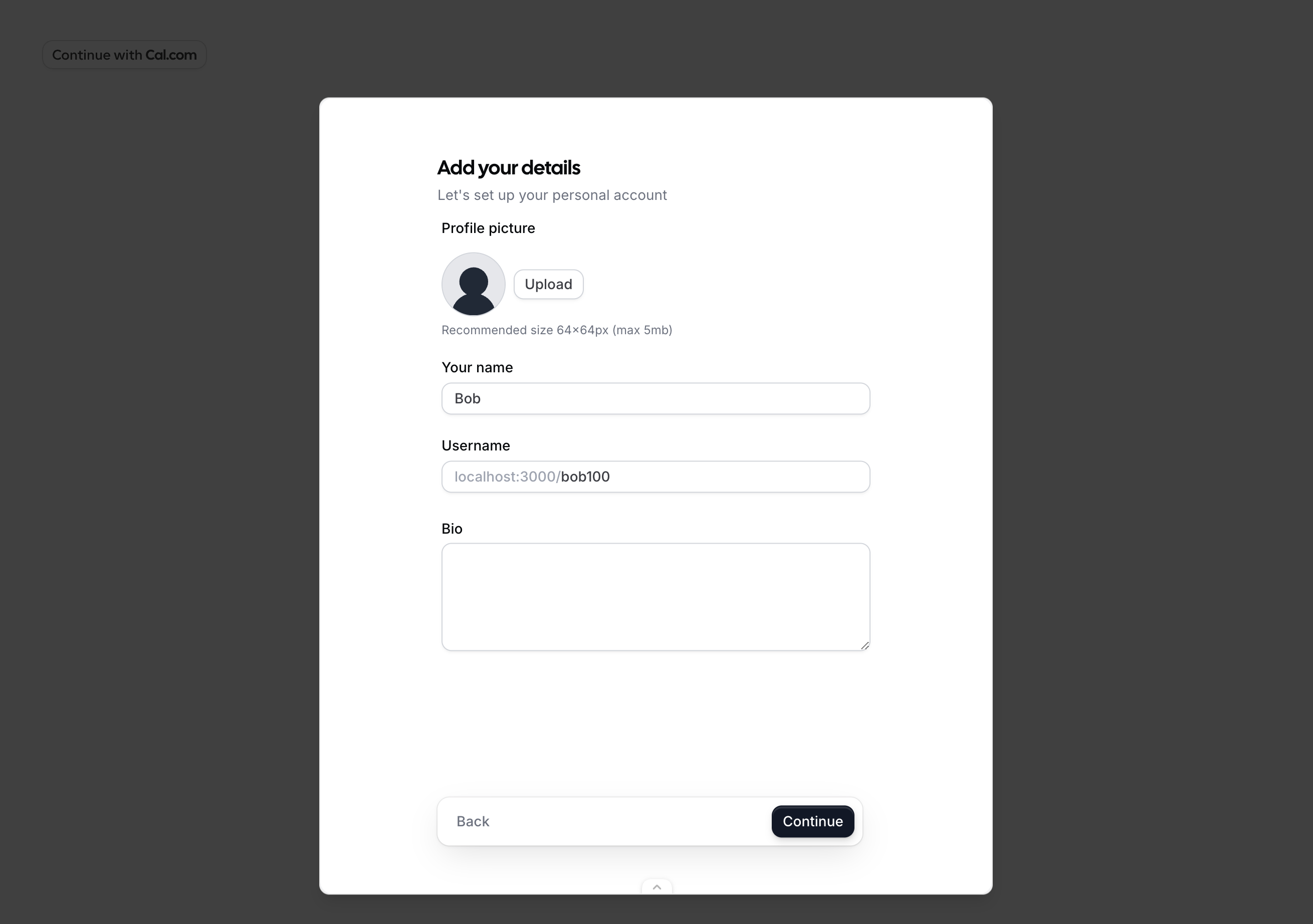
user.name prop prefills the name field.
scope passed to the component.
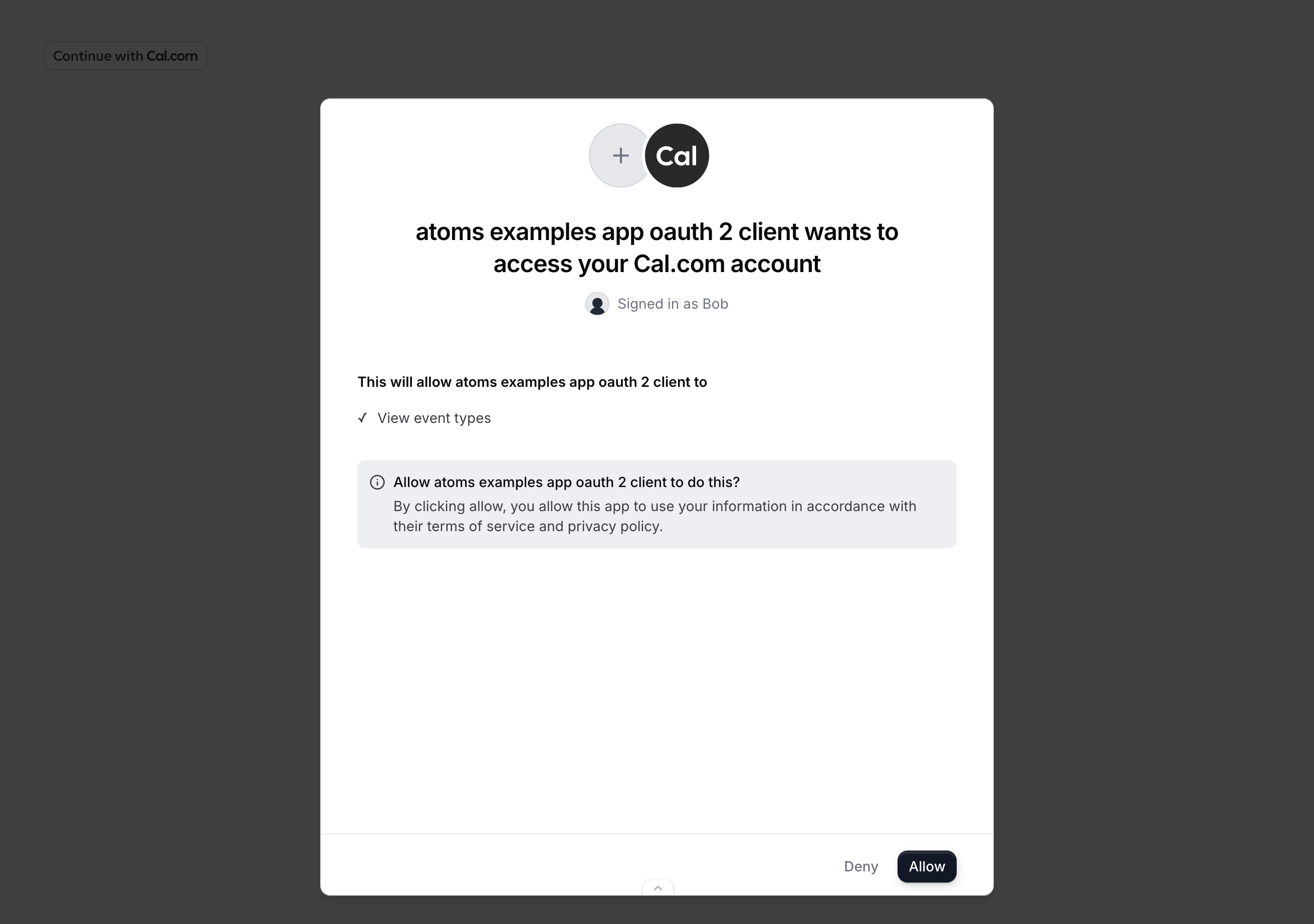
onAuthorizationAllowed fires with the authorization code. Exchange it for tokens using the token endpoint.
Public clients (PKCE)
Public OAuth clients cannot safely store a client secret (e.g. browser-only apps). Use PKCE to secure the authorization code exchange instead. Generate acode_verifier, derive a code_challenge from it, and pass the challenge to OnboardingEmbed. When you receive the authorization code, exchange it with the code_verifier instead of a client secret.
Error handling
TheonError callback receives an error object with the following shape:
| Code | Description |
|---|---|
INVALID_PROPS | Required props are missing or invalid (e.g. oAuthClientId does not exist, redirectUri does not match a registered URI, or required authorization fields are empty). |
SIGNUP_FAILED | Account creation failed. |
ONBOARDING_FAILED | An error occurred during the onboarding steps. |
AUTHORIZATION_FAILED | The user denied access or OAuth consent failed. |
STATE_MISMATCH | The state in the response did not match the state you provided. Possible CSRF attack. |
UNKNOWN | An unexpected error occurred. |
How it works
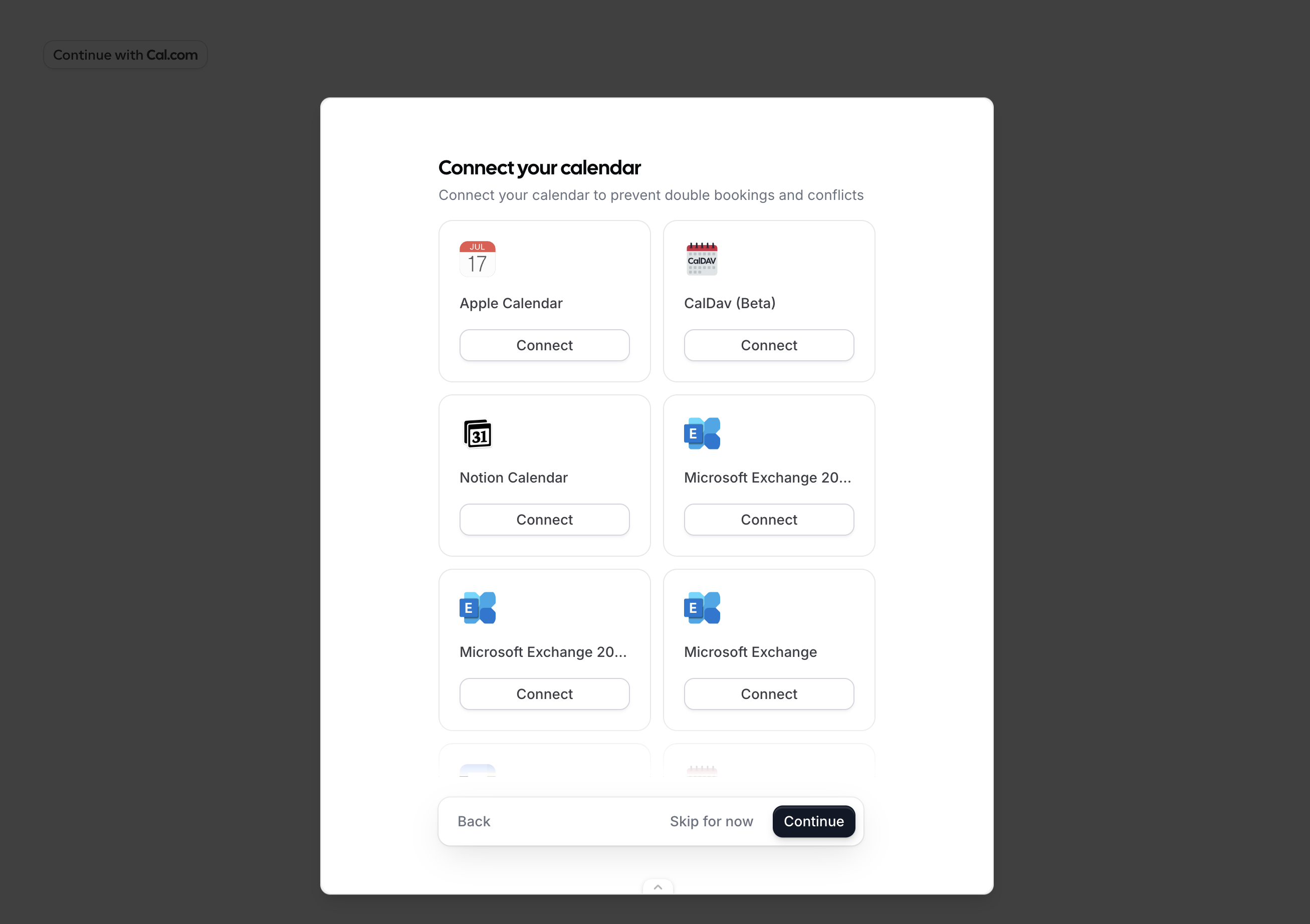
The component opens a dialog containing an iframe that loads Cal.com’s onboarding flow. The iframe runs on Cal.com’s domain with a first-party session, so no third-party cookies are needed. The flow automatically detects the user’s state:- No session — starts at signup/login, then profile setup, calendar connection, and OAuth consent.
- Session with incomplete onboarding — resumes from where the user left off.
- Session with complete onboarding — skips straight to OAuth consent.